VoD is Prone to Content Piracy and Revenue Leakage at Multiple Points, but it is not Impossible to Control
The OTT-video-on-demand (VoD) space has seen exponential growth in recent years, with the Covid-19 pandemic increasing the demand for streaming content even further. Netflix, for example, added a whopping 15.8 million subscribers in the first quarter of 2020 alone, more than double the expected 7.2 million. This has also meant that content piracy has been on the rise and is a major challenge for direct-to-consumer distribution today. A recent report estimated that the global online TV and movie industry is set to collectively lose around USD 51.6 billion in 2022 due to piracy. The losses incurred due to piracy of content to content producers and delivery platforms is, therefore, of paramount importance.
Common Types of VOD Piracy Source
| Type | Label | Description |
|---|---|---|
| Cam | CAM-Rip, CAM, HDCAM | Taken by an audience with a camcorder at theater. Very low quality video and audio. |
| Telesync | TS, HDTS, TELESYNC | Taken by a theater worker in the projection booth. (uncommon) |
| Screener | SCR, DVDSCR, BDSCR | Ripped from early DVD or BD releases for movie reviewers(e.g. Academy members). It is now banned by Academy and Emmy. |
| DVD/Blu-ray Rip | DVDRip, BDRip, BluRay | Encoded(ripped) directly from the output of DVD/Blu-ray disc player. The most common type of VOD leakage until now. |
| Web Rip | WEBRIP, WEB | Extracted from non-DRM streams or recorded via HDMI/HDCP stripper. The reason why DRM and output protection are needed. |
| Web Download | WEBDL, WEB-DL, HDRip | Extracted from VOD streaming and remuxed without re-encoding. The leaked video has the same quality as the source. The reason why hardware DRM is needed. |
VoD formats allow users to access video content at their convenience in a diverse range of devices, ranging from TV sets, personal computers, tablets to mobile phones. This also creates leakage points from where pirates can access the content and push it to peer-to-peer (P2P) space, which is the breeding ground for premium pirated content.
Some of the major factors that contribute to piracy are as follows:
-
Credentials Sharing:
Usually, people buy a single account on OTT platforms, like Netflix and Amazon Prime, and share it with friends and family, which refrains content distributors and creators from reaping the full benefits of their assets. This also opens up the content to pirates. They often steal credentials from authorized users and sell these accounts at cheap prices on the dark or open web. Some common methods of illegal credential sharing are as follows:
- Token theft: Most online SVoD applications and websites use tokens to identify users. Pirates can copy these tokens to other devices and use them illegally to obtain free access to premium content.
- Bypass of concurrency tools: Subscription-based OTT platforms often restrict the number of devices per account. Pirates find a way around these restrictions by hacking into their servers so that more people can access the account without having to pay any fee.
-
Trial Fraud:
Users often exploit the trial policy of a subscription-based service by repeatedly taking up the trial offer using different login credentials.
-
Simulcasting:
This method entails capturing of the content during playback with the intent to redistribute. There are several ways of stream capturing such as:
- Recording screens during playback or screen-share session capturing.
- Using VPN to access content that is not available for a particular geographical area.
- Using video playback softwares or tampering with the Android OS.
- Usage of re-quantization techniques to bypass watermarking in videos.
-
Downloading Content:
These days many tools are freely available on the internet that help users to download content illegally. While almost all streaming platforms use encryption to protect their videos from illegal distribution, users can sometimes easily locate the encryption keys on the internet. Pirates can even hack the storage platforms to get access to unreleased content.
Some of the popular sources and tools used by pirates or unscrupulous users include:
- WEB-DL/WEB DL or HDRip: Using these tools, pirates extract the video (H.264 or H.265) and audio (AC3/AAC) from VoD services and remux them into an MKV container without sacrificing quality.
- WEBRIP: It allows the file to be extracted using the HLS or RTMP/E protocols and remux from a TS, MP4, or FLV container to MKV. Such files are ripped from releases with no or weak DRM.
- WEBCAP: A WEBCap is a rip created by capturing video from a DRM-enabled streaming service.
Since VoD offers multiple entry points to pirates and illegal users, it is considered a more vulnerable medium than live streams. Pirates exploit P2P file-sharing sites through torrents. These sites have even become standardized now in the way in which they offer ripped content to users. For example, a ripped Hollywood production will have a file name on a P2P site like “The.Invisible.Man.2020.HDRip.XviD.B4ND1T9” in the order “movie title.year of release in theaters.type of the source.codec.name of the release group.” Apart from torrent downloads, the other sources of pirated content include web storage portals, illegal sites and apps, add-ons for the Kodi player, and sites likes Popcorn Time that offer torrents and have a built-in media player for free streaming of videos.
Pirates tend to use DVDs, Blu-Ray disks, cam version of theatrical releases, etc. in storage lockers, which are then used to maintain P2P libraries. While the P2P ecosystem offers content to aggregators, the online digital lockers provide access to illegal video content, for use by Kodi pirate add-ons, as well as the online “indexers”, or, websites that aggregate links to the content sources and present them to web users.
Distribution of Pirated Videos
An easy method of selling or distributing illegal content is the hardware sales model. One can simply acquire an Android-based set-top box (STB) or a Fire TV stick, load the open-source Kodi player in it, and load some free pirate-content-enabled add-ons to access free video content. These add-ons are preconfigured to automatically update from their respective repositories each time the Kodi application is launched.
Many users that want to access video streams illegally tend to use modified STB devices, like the MAG series, which are IP-based devices meant for accessing free-to-air content but are altered significantly to access premium content as well. These devices bypass the subscription locks by securely login in to a “stalker portal” for command and control. These portals break the subscription credentials of IPTV feeds and let them be streamed through MAG devices to TVs.
Controlling Piracy
The illegal content distribution networks have developed advertisement-supported revenue streams and are expected to grow significantly. Android-based ad-supported applications can exploit Android emulators without obtaining any new hardware. This lets the developer monetize the platform using ad revenues and even subscriptions.
Despite this sophistication in the piracy ecosystem, all is not lost, and there are several ways to prevent or greatly minimize content piracy. Some of the best practices that can be followed by content owners and distributors to mitigate content theft are as follows:
-
Blocking Credential Sharing:
Streaming websites that use popular content management systems, like WordPress, can install multiple plugins built by their developer communities to stop credential sharing. For other websites, a unique ID can be allocated whenever a user logs in with a particular credential, so that when this ID is active no other ID can be generated for the given account. Content providers can also use single sign-on through Facebook or Google to reduce credential sharing.
-
Encryption:
Video encryption can prevent users from viewing content without permission. Two of the most prominent video encryption protocols are the AES-128 encryption and the HLS encryption with AES-128.
-
Digital Rights Management (DRM):
While content encryption is helpful, the open keys exchange feature can expose the encryption keys. DRM technology works alongside encryption to prevent illegal access to encryption keys.
-
Forensic Watermarking:
While DRM technology protects content during transmission, forensic watermarking helps ensure security at the user’s device. It helps broadcasters add unique identification markers to their content which are not damaged even after transcoding or resizing the video. It also helps identify the source of leakage and take necessary action.
-
Secure Hosting:
Content creators can rely on third-party hosting services to take care of their streaming platforms. These platforms must provide security, robust content delivery networks (CDNs), video analytics, and video API services.
-
IP Restrictions:
IP addresses from various parts of the world can be restricted from accessing content. This helps block anyone including pirates and competitors from a given country.
-
Restricting Video Playback:
Depending on user behavior, content distributors can limit the watch time for users to reduce account sharing.
Piracy is a major concern for content creators and broadcasters and leads to huge losses in revenue for the content industry each year. Securing VoD content, therefore, necessitates a thorough understanding of how piracy takes place and identifying the best countermeasures to eliminate maximum possible threat. While piracy through credential sharing, cam recording, and illegal web distribution by third parties is on the rise, measures such as multi-DRM SaaS, forensic watermarking, IP restrictions, etc. and choosing a trustworthy VoD platform provider can help keep pirates at bay.

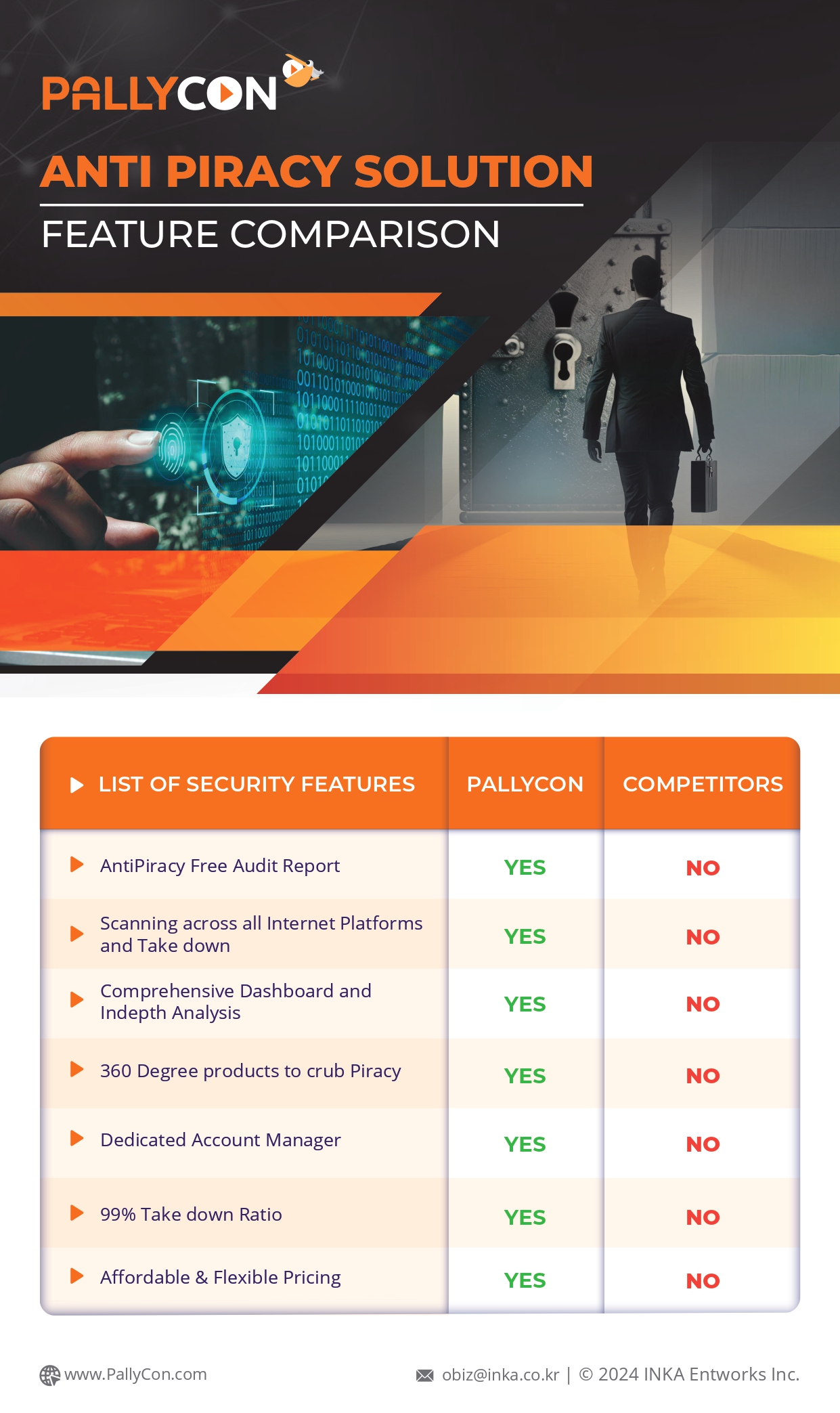
PallyCon provides cloud-based SaaS multi-DRM solution and Forensic Watermarking service. Cloud services built on AWS enables you to use services in the cloud. Get started contents protection quickly and easily with PallyCon.